Which Approach Is Intended To Prevent Exploits That Target Syslog - Use a vpn between a syslog client and the syslog server. Configuring firewalls to block incoming and outgoing traffic on syslog. Use a vpn between a syslog client and the syslog server. Which approach is intended to prevent exploits that target syslog? Which approach is intended to prevent exploits that target syslog? Which approach is intended to prevent exploits that target syslog?
Use a vpn between a syslog client and the syslog server. Which approach is intended to prevent exploits that target syslog? Which approach is intended to prevent exploits that target syslog? Use a vpn between a syslog client and the syslog server. Which approach is intended to prevent exploits that target syslog? Configuring firewalls to block incoming and outgoing traffic on syslog.
Use a vpn between a syslog client and the syslog server. Use a vpn between a syslog client and the syslog server. Which approach is intended to prevent exploits that target syslog? Which approach is intended to prevent exploits that target syslog? Which approach is intended to prevent exploits that target syslog? Configuring firewalls to block incoming and outgoing traffic on syslog.
SolarWinds Kiwi Syslog Server A versatile syslog solution 4sysops
Use a vpn between a syslog client and the syslog server. Which approach is intended to prevent exploits that target syslog? Which approach is intended to prevent exploits that target syslog? Configuring firewalls to block incoming and outgoing traffic on syslog. Which approach is intended to prevent exploits that target syslog?
Protecting Against SharePoint Exploits Why Businesses Need AppGuard
Which approach is intended to prevent exploits that target syslog? Which approach is intended to prevent exploits that target syslog? Configuring firewalls to block incoming and outgoing traffic on syslog. Use a vpn between a syslog client and the syslog server. Which approach is intended to prevent exploits that target syslog?
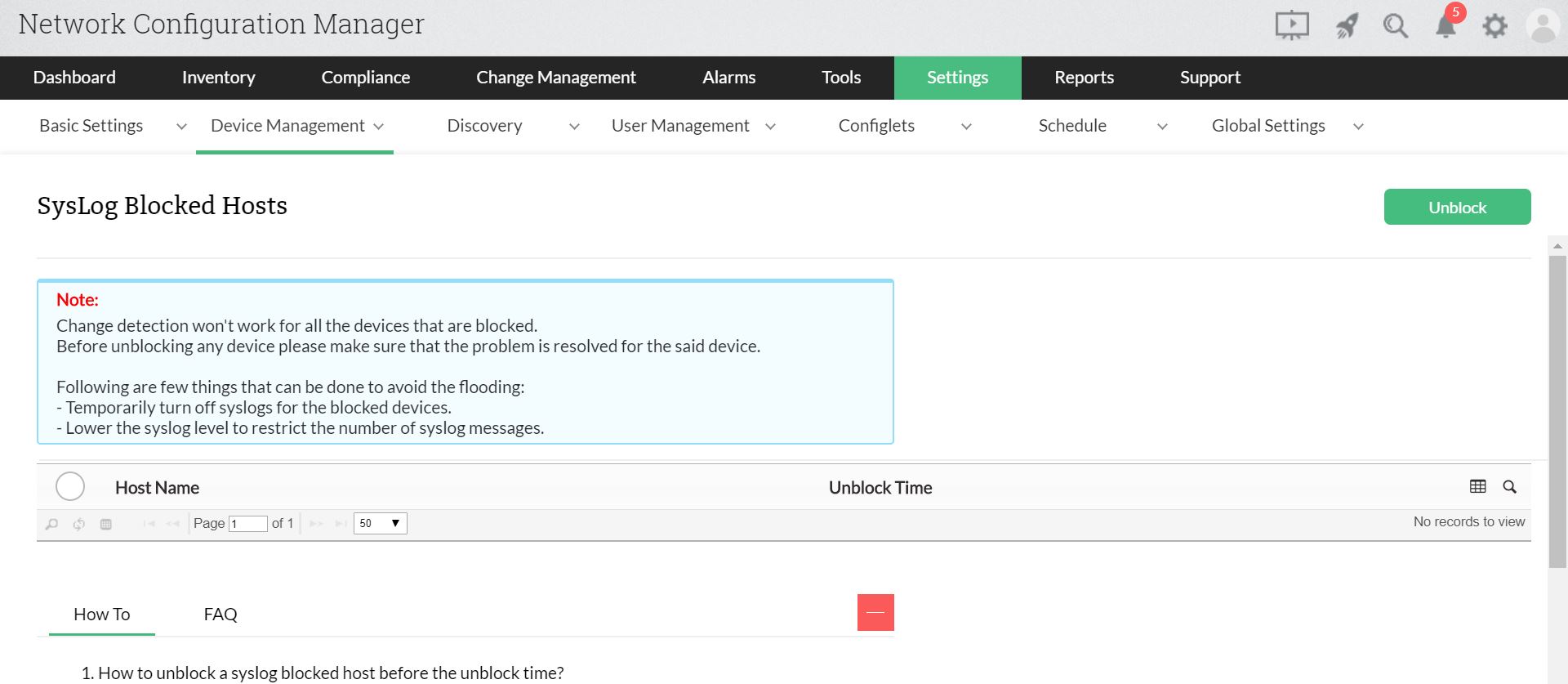
Syslog Flood Prevention v12 Network Configuration Manager Help
Configuring firewalls to block incoming and outgoing traffic on syslog. Which approach is intended to prevent exploits that target syslog? Which approach is intended to prevent exploits that target syslog? Use a vpn between a syslog client and the syslog server. Use a vpn between a syslog client and the syslog server.
Scaling Syslog The Challenge That Never Goes Away Cribl
Use a vpn between a syslog client and the syslog server. Configuring firewalls to block incoming and outgoing traffic on syslog. Which approach is intended to prevent exploits that target syslog? Use a vpn between a syslog client and the syslog server. Which approach is intended to prevent exploits that target syslog?
Wave of Exploits Target Ivanti Devices’ Latest Security Vulnerability
Which approach is intended to prevent exploits that target syslog? Use a vpn between a syslog client and the syslog server. Use a vpn between a syslog client and the syslog server. Which approach is intended to prevent exploits that target syslog? Configuring firewalls to block incoming and outgoing traffic on syslog.
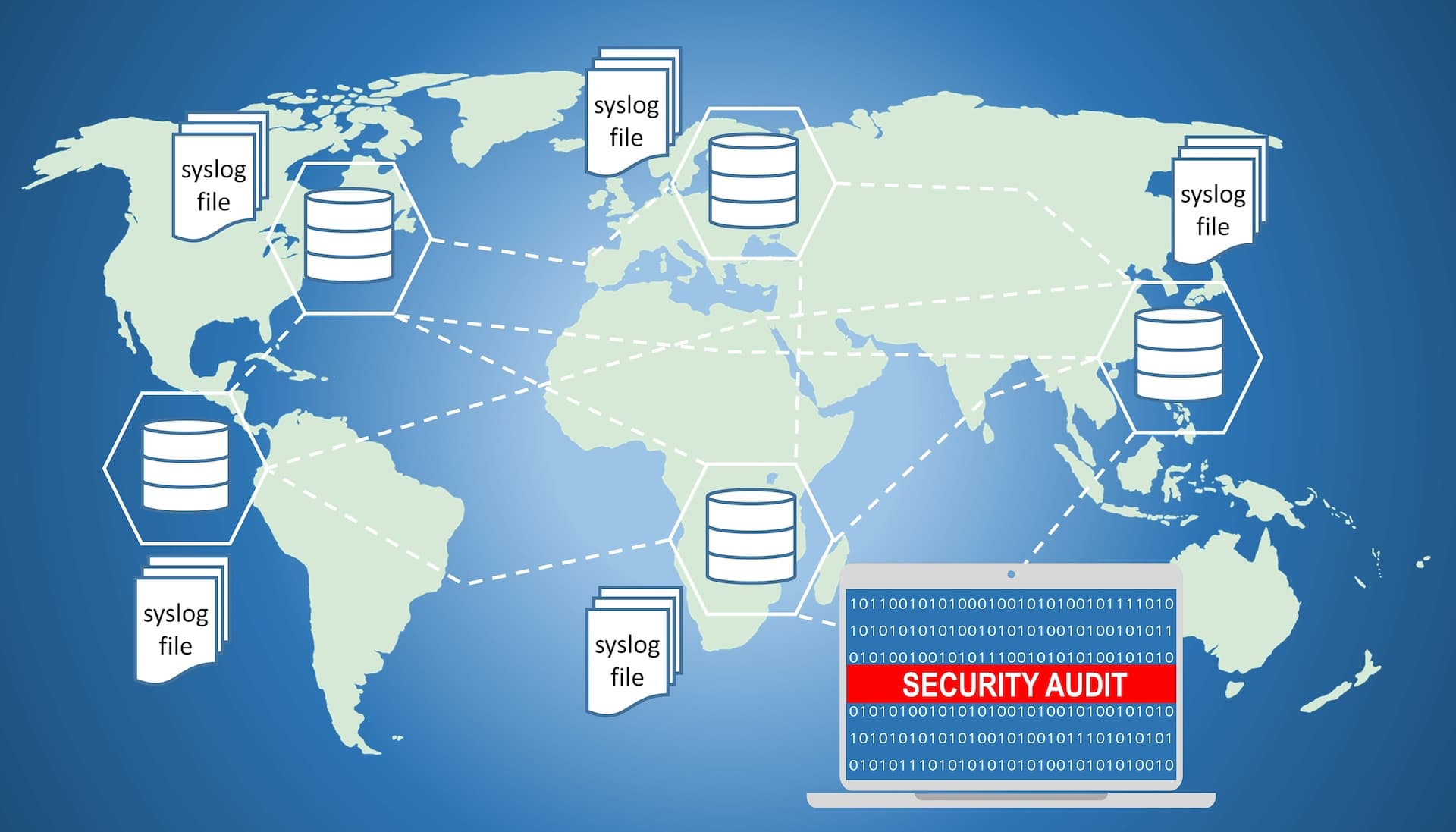
What is syslog? LogicMonitor
Which approach is intended to prevent exploits that target syslog? Which approach is intended to prevent exploits that target syslog? Use a vpn between a syslog client and the syslog server. Use a vpn between a syslog client and the syslog server. Configuring firewalls to block incoming and outgoing traffic on syslog.
How can I prevent my syslogng server from pinning to a single stream
Which approach is intended to prevent exploits that target syslog? Use a vpn between a syslog client and the syslog server. Which approach is intended to prevent exploits that target syslog? Which approach is intended to prevent exploits that target syslog? Configuring firewalls to block incoming and outgoing traffic on syslog.
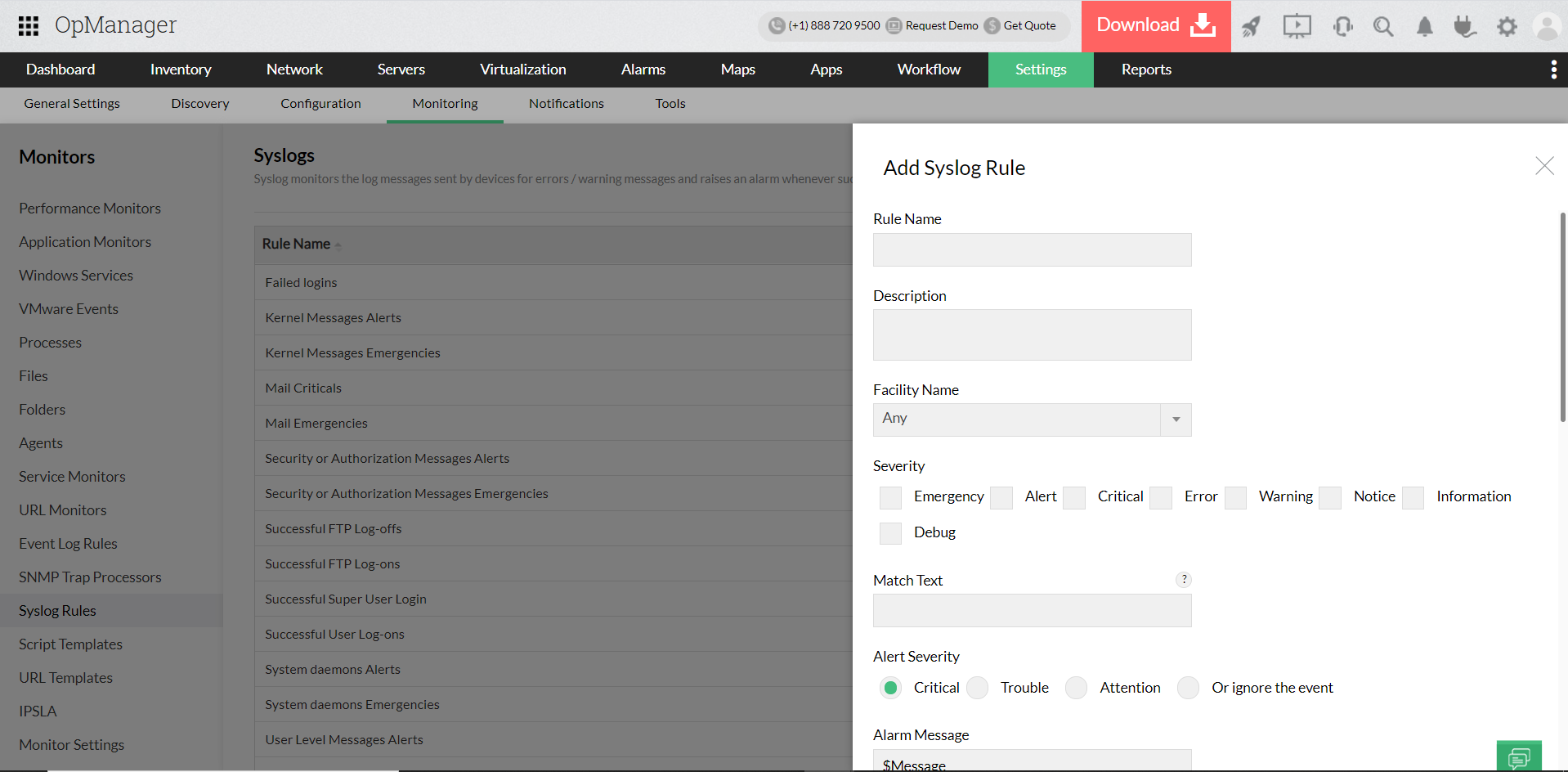
Syslog monitoring Rulebased syslog monitor OpManager
Which approach is intended to prevent exploits that target syslog? Which approach is intended to prevent exploits that target syslog? Which approach is intended to prevent exploits that target syslog? Use a vpn between a syslog client and the syslog server. Configuring firewalls to block incoming and outgoing traffic on syslog.
Syslog An Introduction, Part 1
Use a vpn between a syslog client and the syslog server. Which approach is intended to prevent exploits that target syslog? Use a vpn between a syslog client and the syslog server. Configuring firewalls to block incoming and outgoing traffic on syslog. Which approach is intended to prevent exploits that target syslog?
What is Exploit? Types of Exploits And How They Work. Gridinsoft
Which approach is intended to prevent exploits that target syslog? Which approach is intended to prevent exploits that target syslog? Which approach is intended to prevent exploits that target syslog? Configuring firewalls to block incoming and outgoing traffic on syslog. Use a vpn between a syslog client and the syslog server.
Which Approach Is Intended To Prevent Exploits That Target Syslog?
Configuring firewalls to block incoming and outgoing traffic on syslog. Which approach is intended to prevent exploits that target syslog? Use a vpn between a syslog client and the syslog server. Use a vpn between a syslog client and the syslog server.